SSH IoT Behind Firewall: The Ultimate Guide For Smart Devices
Hey there, tech enthusiasts! If you're diving into the world of IoT (Internet of Things) and wondering how SSH can help secure your smart devices behind a firewall, you've come to the right place. SSH IoT behind firewall is more than just a buzzword; it's a critical concept that every modern tech-savvy individual should know. In this guide, we'll break down everything you need to understand about securing your IoT devices with SSH while ensuring they stay protected behind firewalls.
As more and more devices connect to the internet, the risk of cyber threats increases exponentially. From smart thermostats to security cameras, these gadgets are vulnerable to hacking if not properly secured. That's where SSH comes in, acting as a digital bodyguard for your IoT devices. In this article, we'll explore how SSH works, why it's essential, and how you can implement it effectively behind firewalls.
So, buckle up and let's dive deep into the world of SSH and IoT. Whether you're a beginner or an advanced user, this guide will provide you with the tools and knowledge you need to protect your smart devices like a pro. Let's get started!
Read also:Amber Daniels The Rising Star Shining Brighter Every Day
Here's a quick table of contents to help you navigate through the article:
- What is SSH?
- IoT Security Challenges
- SSH IoT Behind Firewall
- How to Secure IoT Devices
- Best Practices for SSH IoT
- Firewall Basics
- Tools and Software for SSH
- Real-World Examples
- Frequently Asked Questions
- Conclusion
What is SSH?
Alright, let's start with the basics. SSH, or Secure Shell, is a cryptographic protocol used to secure communications over a network. Think of it as a secure tunnel that allows you to remotely access and manage devices without exposing sensitive data to prying eyes. SSH ensures that your data remains encrypted and protected from unauthorized access.
Now, when it comes to IoT, SSH plays a crucial role in securing devices that are connected to the internet. By using SSH, you can establish a secure connection between your devices and a server, ensuring that your data stays safe even when traversing through firewalls.
Why SSH Matters for IoT
Here's the deal: IoT devices are often left unprotected, making them easy targets for hackers. SSH helps bridge this gap by providing a secure communication channel. Whether you're managing a smart home or monitoring industrial equipment, SSH ensures that your data remains private and secure.
IoT Security Challenges
Let's face it, securing IoT devices isn't as straightforward as securing a laptop or smartphone. These devices often lack robust security features, making them vulnerable to attacks. Some of the common challenges include:
- Limited processing power
- Outdated firmware
- Weak default passwords
- Lack of encryption
These challenges make it essential to implement additional security measures, such as SSH, to protect your devices. Without proper security, your IoT devices could become entry points for hackers to access your network.
Read also:Charlie Sheen 2025 The Untold Story And Whatrsquos Coming Next
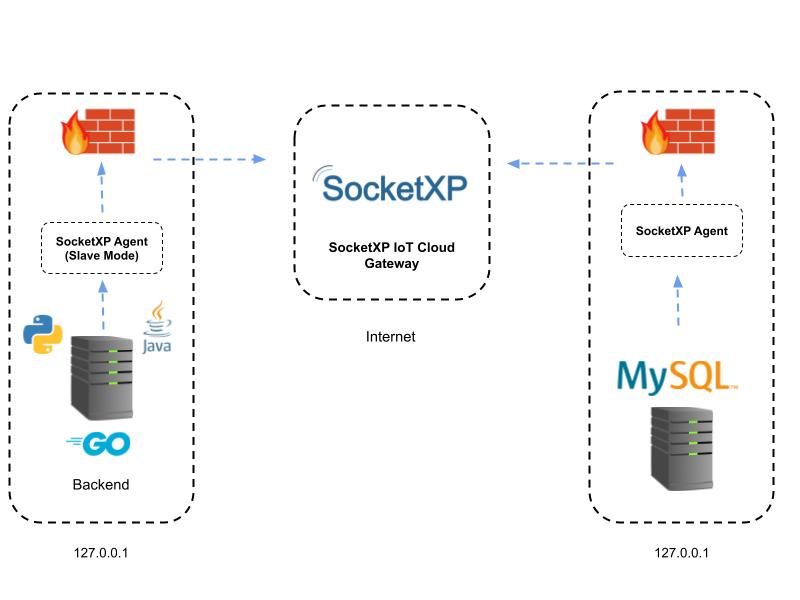
SSH IoT Behind Firewall
Now, here's where things get interesting. When you place IoT devices behind a firewall, you add an extra layer of protection. A firewall acts as a gatekeeper, controlling incoming and outgoing traffic to and from your network. By combining SSH with a firewall, you create a robust security framework that keeps your devices safe.
How SSH Works Behind a Firewall
SSH operates by creating an encrypted connection between your device and a server. When you place your IoT devices behind a firewall, you can configure the firewall to allow only specific SSH traffic. This ensures that only authorized devices can communicate with your network, reducing the risk of unauthorized access.
How to Secure IoT Devices
Securing IoT devices goes beyond just using SSH. Here are some additional steps you can take to enhance the security of your devices:
- Change default passwords
- Keep firmware up to date
- Use strong encryption protocols
- Limit network access
By following these best practices, you can significantly reduce the risk of cyberattacks on your IoT devices. Remember, security is a continuous process, so stay vigilant and keep updating your devices regularly.
Best Practices for SSH IoT
When it comes to implementing SSH for IoT devices, there are a few best practices you should follow:
- Use strong authentication methods
- Enable key-based authentication
- Disable password authentication
- Restrict SSH access to specific IP addresses
These practices ensure that only authorized users can access your devices via SSH, further enhancing the security of your network.
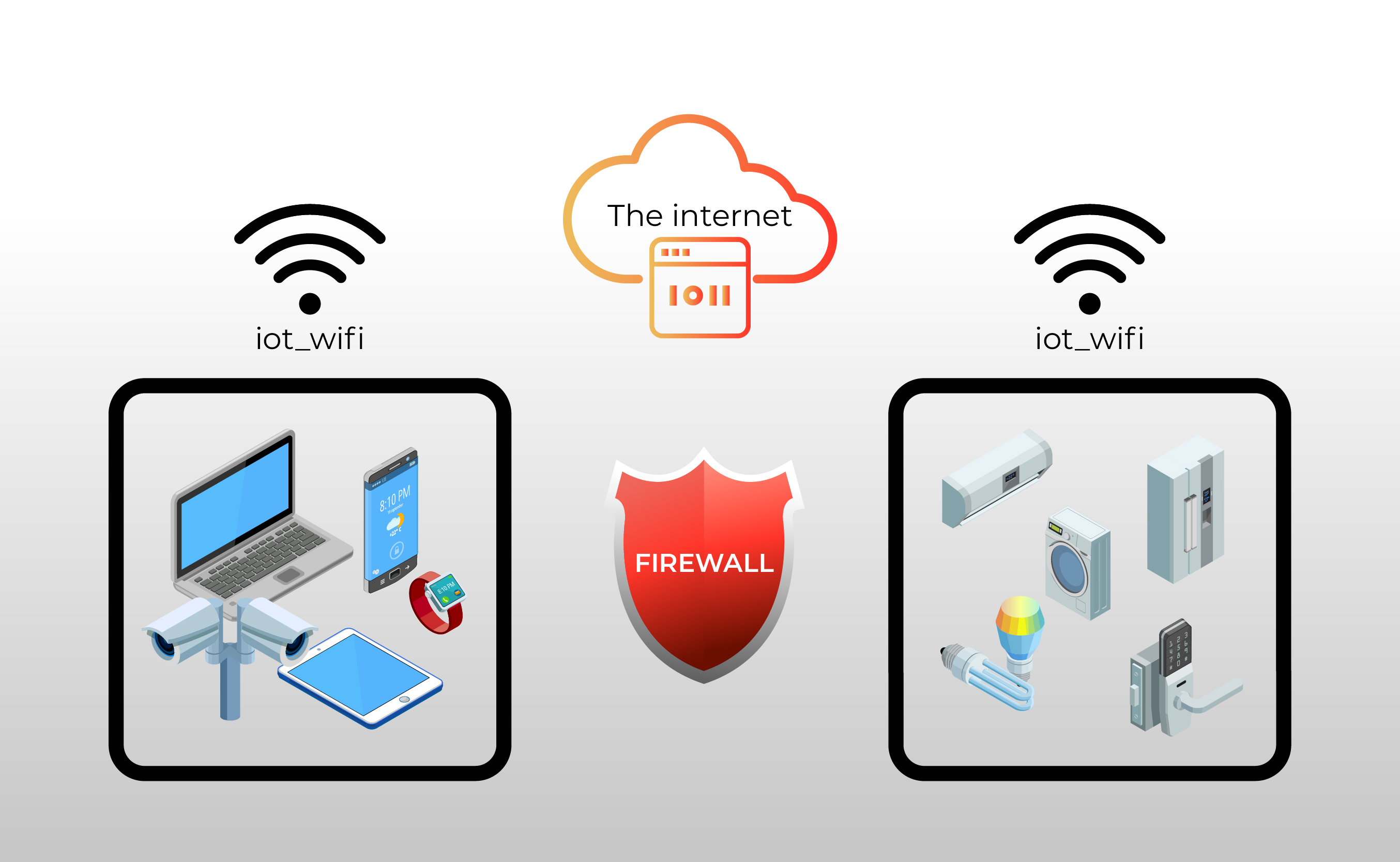
Firewall Basics
Before we dive deeper into SSH, let's talk about firewalls. A firewall is a network security system that monitors and controls incoming and outgoing traffic based on predetermined security rules. It acts as a barrier between your network and the outside world, preventing unauthorized access.
When configuring a firewall for IoT devices, it's important to set up rules that allow only necessary traffic. This ensures that your devices remain protected while still being able to communicate with the outside world.
Tools and Software for SSH
There are several tools and software available that can help you implement SSH for your IoT devices. Some popular options include:
- OpenSSH
- Putty
- WinSCP
These tools provide user-friendly interfaces and advanced features that make it easy to manage SSH connections. Whether you're a beginner or an advanced user, these tools have something to offer.
Real-World Examples
To give you a better understanding of how SSH can be used to secure IoT devices, let's look at a few real-world examples:
Smart Home Security
Imagine you have a smart home security system that uses cameras to monitor your property. By using SSH, you can securely access these cameras from anywhere in the world, ensuring that your data remains private and secure.
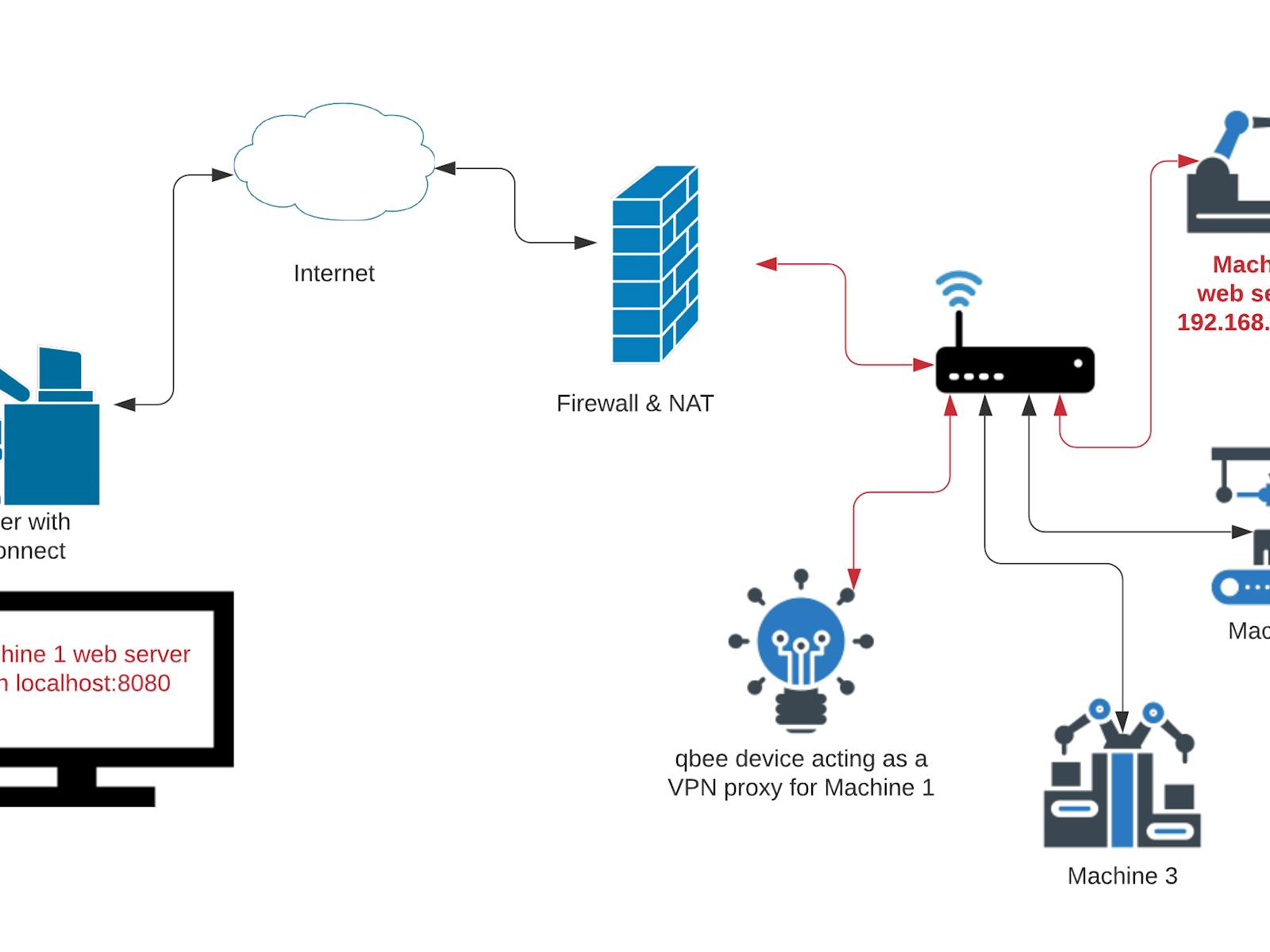
Industrial IoT
In industrial settings, IoT devices are often used to monitor and control critical infrastructure. SSH provides a secure way to manage these devices remotely, ensuring that your operations run smoothly without the risk of cyberattacks.
Frequently Asked Questions
Here are some common questions people have about SSH and IoT:
Can SSH protect against all types of cyberattacks?
While SSH provides strong protection against unauthorized access, it's not a silver bullet. You should combine SSH with other security measures, such as firewalls and antivirus software, to create a comprehensive security strategy.
Is SSH difficult to implement?
Not at all! With the right tools and software, implementing SSH for IoT devices is relatively straightforward. Plus, there are plenty of resources available online to help you get started.
Conclusion
There you have it, folks! SSH IoT behind firewall is a powerful concept that can significantly enhance the security of your smart devices. By understanding how SSH works and implementing best practices, you can protect your network from cyber threats and ensure that your data remains safe.
So, what are you waiting for? Start securing your IoT devices today and take the first step towards a safer, smarter future. Don't forget to leave a comment or share this article with your friends. Together, we can make the internet a safer place for everyone!
Article Recommendations